Edit your AD/OpenLDAP integration
In this topic, you will learn how to edit your Portnox™ Cloud integration with local Active Directory or OpenLDAP. You will also learn about the meaning of additional options for this integration.
Before you begin, you must have a working integration with a local Active Directory or OpenLDAP instance:
To create an integration with a local Active Directory, read the following topic: Integrate with Active Directory.
To create an integration with a local OpenLDAP directory, read the following topic: Integrate with OpenLDAP.
-
In the Cloud portal top menu, click on the Settings option.
-
In the Cloud portal left-hand side menu, click on the Authentication Repositories > DIRECTORY INTEGRATION SERVICE > Directory Domains option.
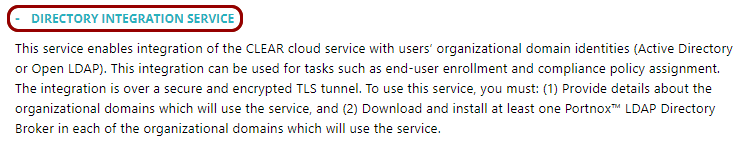
The browser displays the configurations of your local Active Directory and/or OpenLDAP integrations under the DIRECTORY INTEGRATION SERVICE heading and description.
-
Click on the links on the right-hand side of the selected domain entry to perform the following actions:
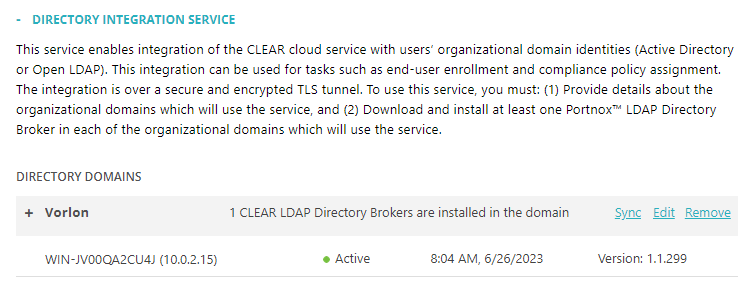
Click on the Sync link to synchronize Portnox Cloud with the directory.
Click on the Edit link to edit the domain configuration.
Click on the Remove link to completely remove the domain configuration.
-
If you clicked on the Edit link, change the settings as required.
Most settings were entered when you created the local Active Directory or OpenLDAP directory integration. In this topic, we explain the additional options.
-
If you want to allow life cycle synchronization, click on the Allow life cycle synchronization checkbox to activate it.
Life cycle synchronization means that Portnox Cloud will react to changes in the directory. For example, if this setting is on, and if you disable or delete an Active Directory or OpenLDAP user, all the devices associated with this user will be unregistered from Cloud. If this setting is off, you will have to unregister devices manually or wait until the retention period expires. By default, life cycle synchronization is on.
-
If you want to turn on mapping based on organizational units, click on the Use OU-based mapping checkbox to activate it.
If this setting is on, whenever you select Active Directory or OpenLDAP groups in Portnox Cloud, you will also have a list of organizational units to select from. If you select entries both from groups and organizational units, and some users are in both the selected groups and organizational units, when onboarding the user, Portnox Cloud will prioritize the authorization details of the group over those of the organizational unit.
-
(Active Directory only) If you want to authenticate devices using the NTLMv2 protocol only, click on the Support NTLMv2 (Experimental) checkbox to activate it.
 Important:By default, LDAP Broker uses standard NTLM authentication, and the user account used to connect to the domain controller only requires standard read-only access to the directory. If you activate this checkbox, NTLMv1 will be disabled and LDAP Broker will use NTLMv2 only. This increases authentication security but requires additional privileges for the user account.
Important:By default, LDAP Broker uses standard NTLM authentication, and the user account used to connect to the domain controller only requires standard read-only access to the directory. If you activate this checkbox, NTLMv1 will be disabled and LDAP Broker will use NTLMv2 only. This increases authentication security but requires additional privileges for the user account.If using NTLMv2, the user account requires additional Active Directory permissions. You can either use a dedicated service account with the following permissions: DS-Replication-Get-Changes and DS-Replication-Get-Changes-All, or add the account to the Domain Admins security group. Note that both options grant sensitive Active Directory privileges and should be reviewed with your AD security team. Without these permissions, all NTLMv2 authentication attempts will fail.
-
In the ADVANCED CONFIGURATION section, you can activate the Use Synchronization Remapping Safeguard option. This prevents Portnox Cloud from deleting synchronized data on the Cloud side if synchronization issues or other problems cause Cloud to assume that objects such as users or devices no longer exist in the authentication directory.
If this setting is enabled and Cloud detects that objects are missing from the authentication directory but still exist in the Cloud database, an alert message is generated. You then have 24 hours to review the change and determine whether the object was intentionally deleted or whether the discrepancy was caused by a synchronization issue, such as a changed password or another error.
Be aware that enabling this setting protects against unintended deletions due to synchronization problems, but it also has implications. If a user or device is intentionally deleted from the authentication directory, Portnox Cloud cannot immediately determine whether the deletion was intentional or caused by a synchronization error. As a result, the user or device will still be able to authenticate to the network for 24 hours. If your security policies require immediate revocation of network access for deleted users or devices, this setting may not be appropriate.
-
-
Click on the Save button to save your changes or click on the
Cancel button to abandon all changes.

After you click on one of the buttons, Portnox Cloud will exit the edit mode.
