Integrate Synology NAS with Zero Trust Network Access
In this topic, you will find general instructions on how to integrate a Synology NAS with Portnox™ Zero Trust Network Access.
Prerequisites:
-
Your Synology NAS must be accessible using a domain name.
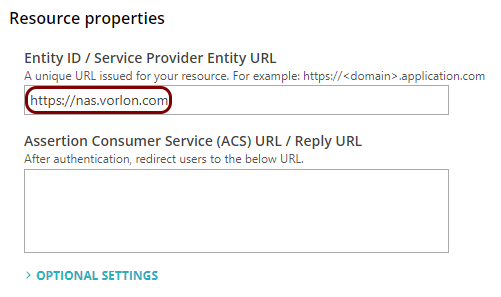
SAML integration does not work with an IP address alone. This is because the SAML configuration uses the domain name as the Entity ID.
To give your Synology NAS a domain name, use one of these options:
-
Use a local DNS server.
-
Create a hosted ZTNA configuration for the NAS. This also lets remote employees access the on-premises NAS without a VPN.
A hosted ZTNA configuration lets you use your own domain name, or it automatically assigns a portnox.com subdomain, which you can use as the Entity ID in your SAML configuration.
You can configure the domain for your Synology NAS by clicking on the Control Panel icon, then clicking on the Login Portal icon, and entering the domain name in the Customized domain field.
-
-
We strongly recommend integrating your Synology NAS with your authentication repository, such as Entra ID or Google Workspace.
-
If you integrate with your repository using LDAP:
-
User accounts are synchronized directly from your repository, so usernames stay consistent automatically. No additional configuration is needed for username mapping.
-
Entra ID: You must use Microsoft Entra Domain Services – a separate paid Azure service that provides a managed LDAP endpoint and syncs users from Entra ID.
-
Google Workspace: LDAP integration requires the Secure LDAP service, which is not available on Business Starter or Business Standard plans. It is available on Business Plus and all Enterprise and Education plans.
-
-
If you do not integrate with your repository:
-
You must create all NAS users manually. You cannot use the @ symbol in the names of users created manually. We strongly recommend that you use the same username as in user emails. For example, create a user kosh if their company email is kosh@vorlon.com.
-
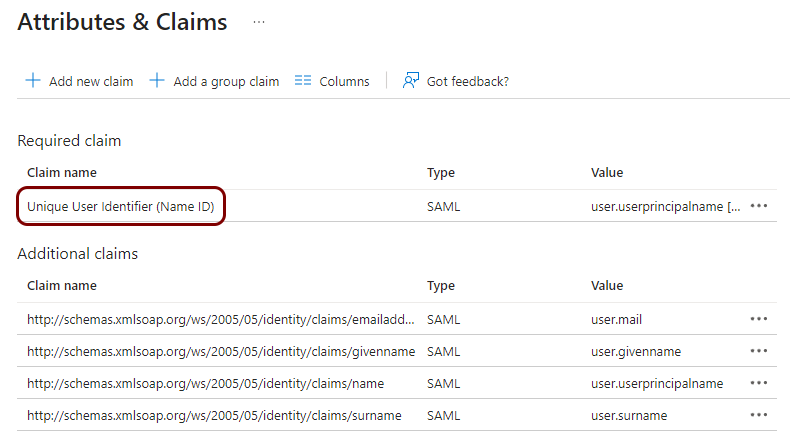
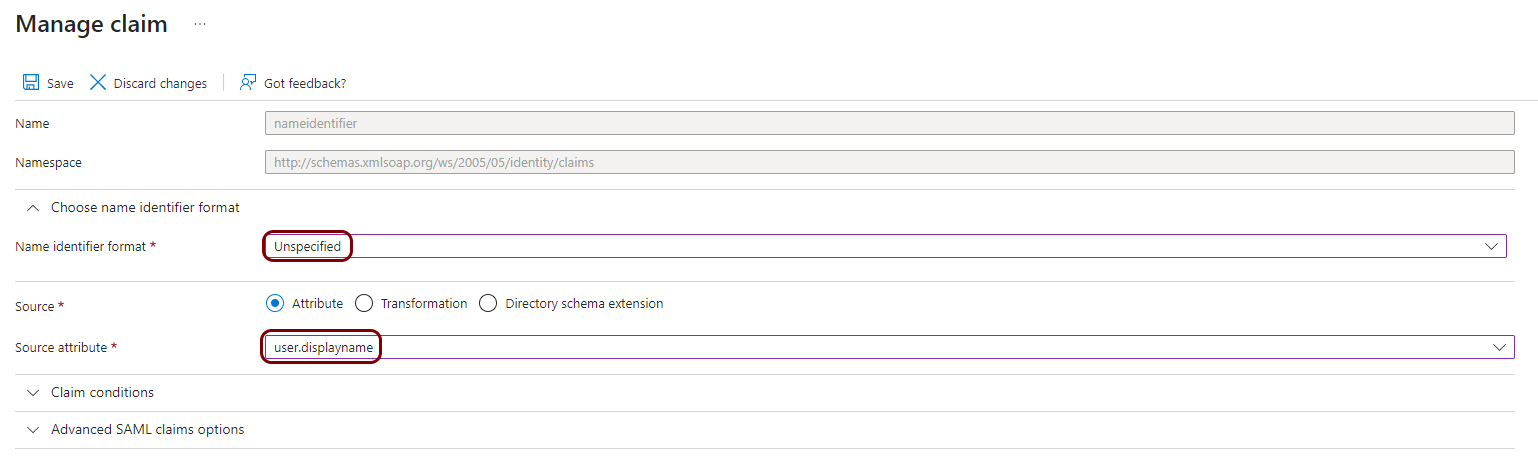
You must create a separate Identity Provider configuration in Portnox Cloud – for example, Entra ID or Google Workspace. This is because Synology NAS requires the NameID claim to contain the Synology username. How you provide this depends on your repository:
-
Entra ID provides a Display Name attribute, which stores the username without the domain part (for example, kosh from kosh@vorlon.com). You can map this attribute directly to the NameID claim, so no custom fields are needed.
-
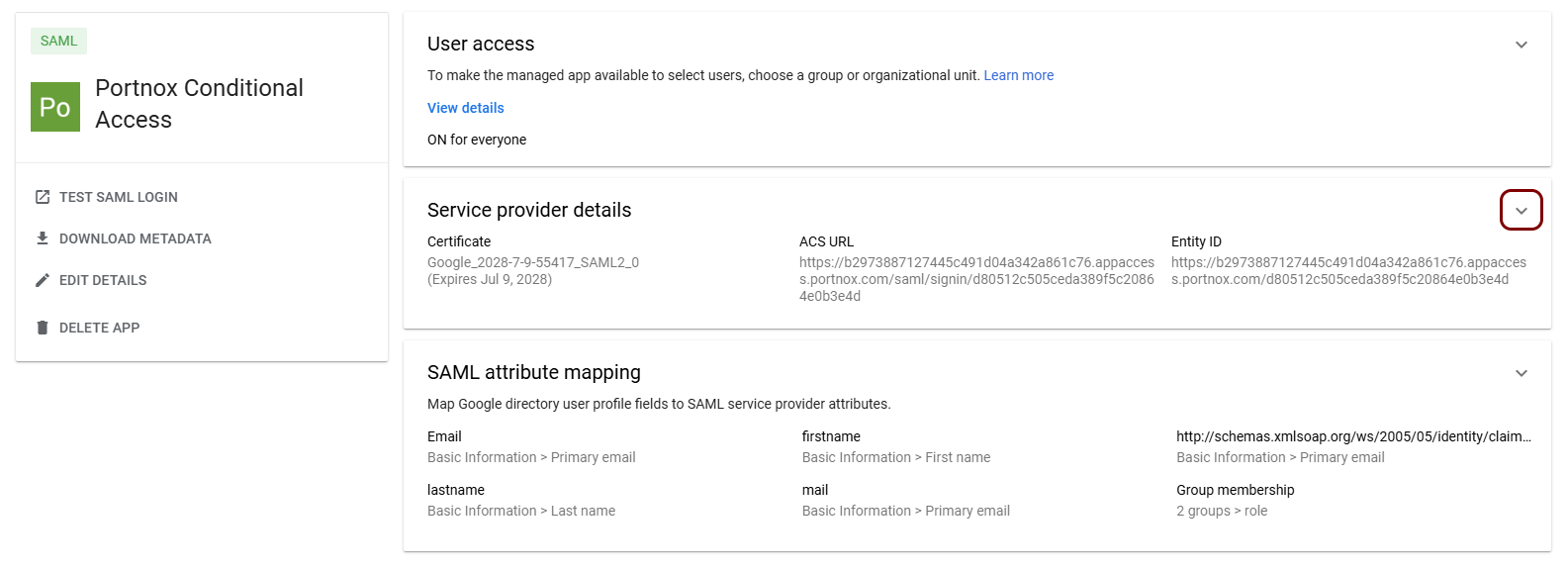
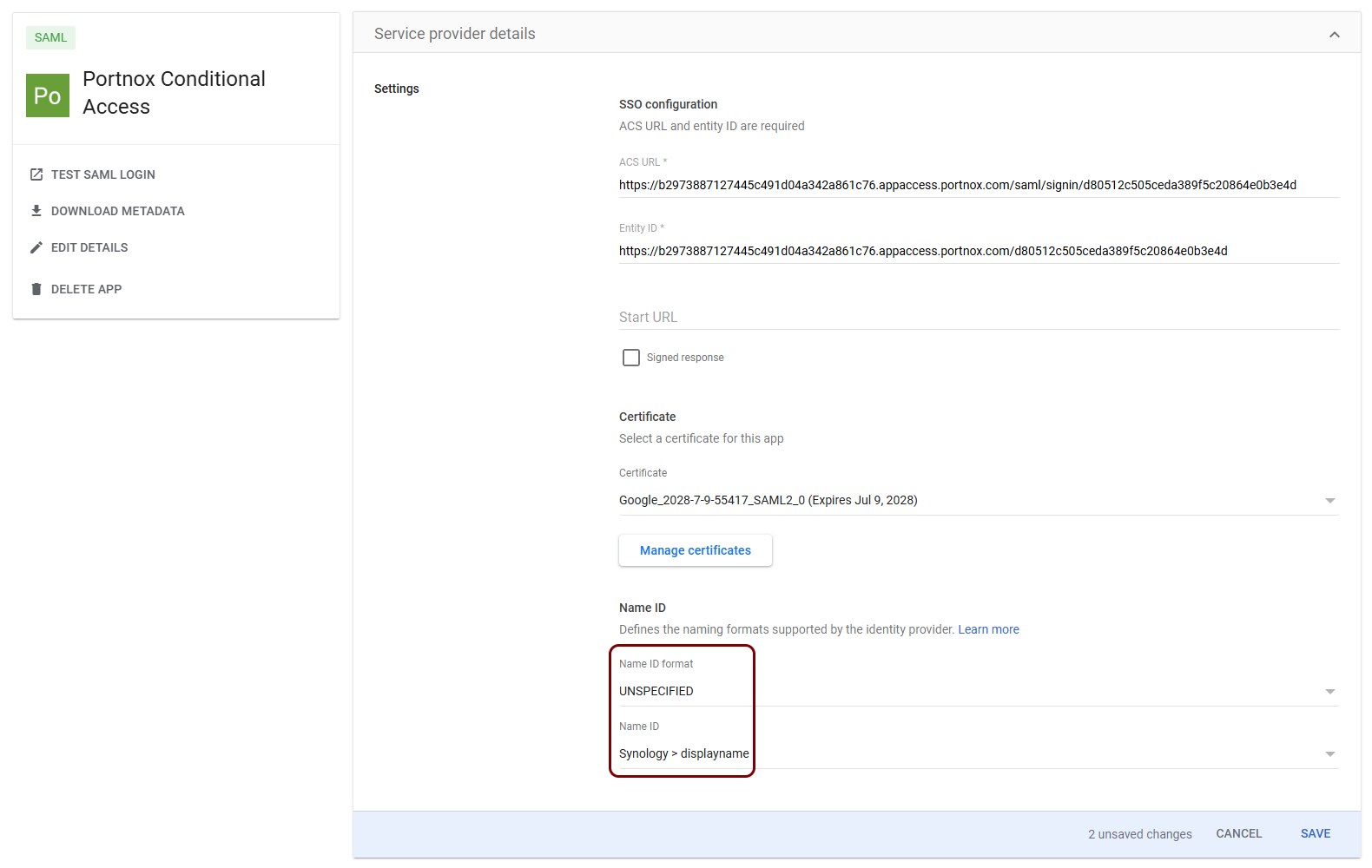
The Google Workspace repository only contains fields for email address, first name, and last name. It has no fields that store the username without the domain part, and there is no function to obtain it automatically. Therefore, you must create a custom field in Google Workspace (for example, Displayname) and manually fill it for every user that needs access to the Synology NAS.
-
-
-
Assumptions for this guide:
-
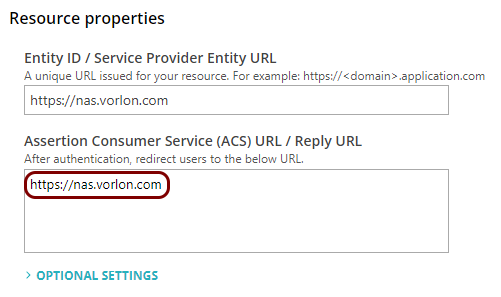
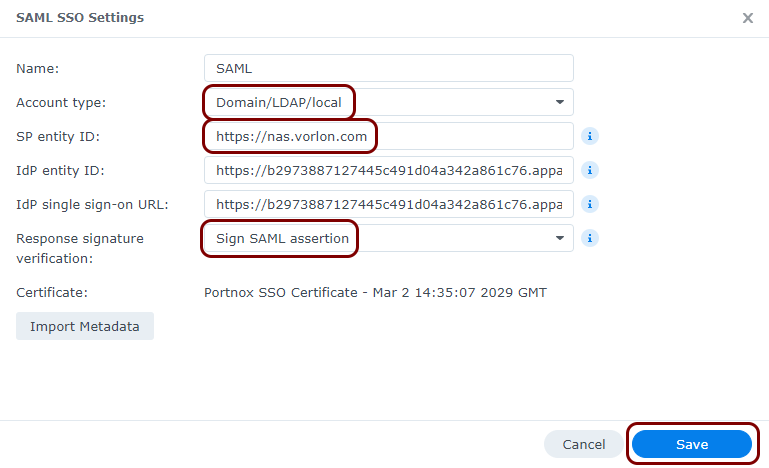
We assume that you use a local DNS server or your own domain in a hosted ZTNA configuration, and that your NAS has the domain name: nas.vorlon.com.
-
We assume that you did not integrate with the repository using LDAP and that you used the same usernames for Synology users as your users’ emails. We will show you how to create and configure custom claims.
Integrating a Synology NAS with an LDAP service provided by Entra ID or Google Workspace is a complex process that is outside the scope of this guide, as it is unrelated to SAML and ZTNA. If you integrated with your repository using LDAP, do not create a new IdP and do not add any custom claims, as the NAS will work with your default IdP and claims configuration.
Create a new identity provider configuration to support Synology
In this section, you will create a new identity provider configuration for Synology NAS and configure its claims.
-
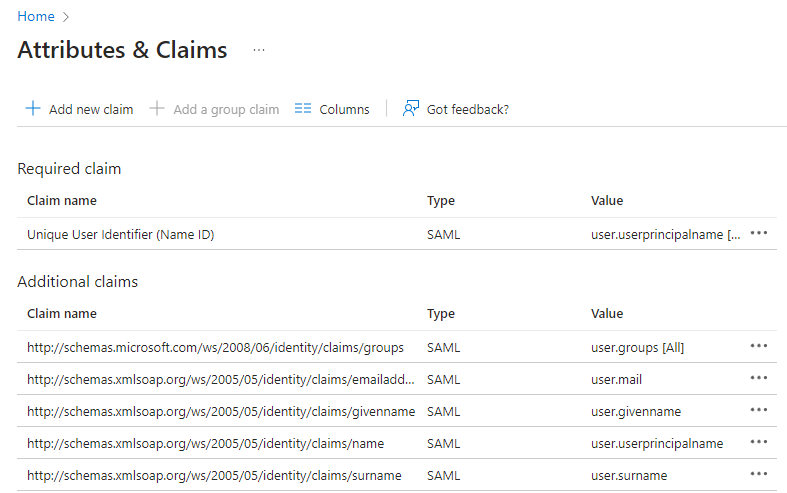
If you use Entra ID, open your Synology ZTNA application configuration and do the following steps.
-
If you use Google Workspace, open your configuration and do the following steps.
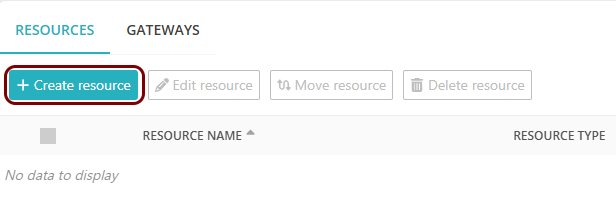
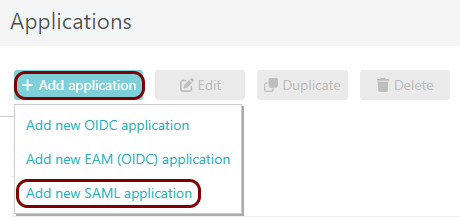
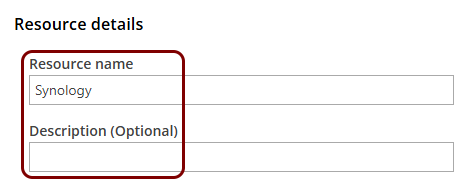
Create a Portnox Cloud application configuration
In this step, you will create a configuration in Portnox Cloud that will contain all the information necessary to integrate with Synology.
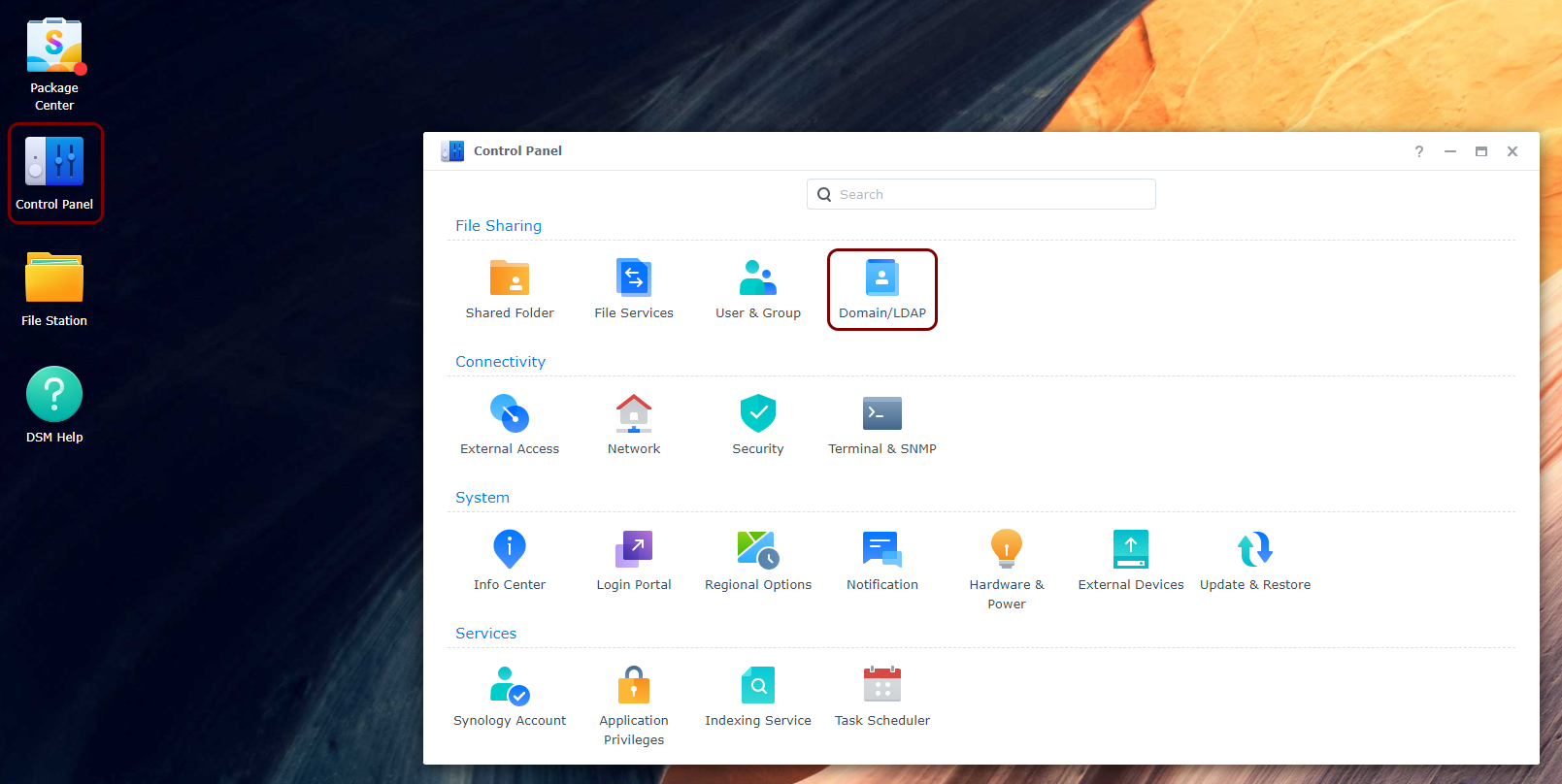
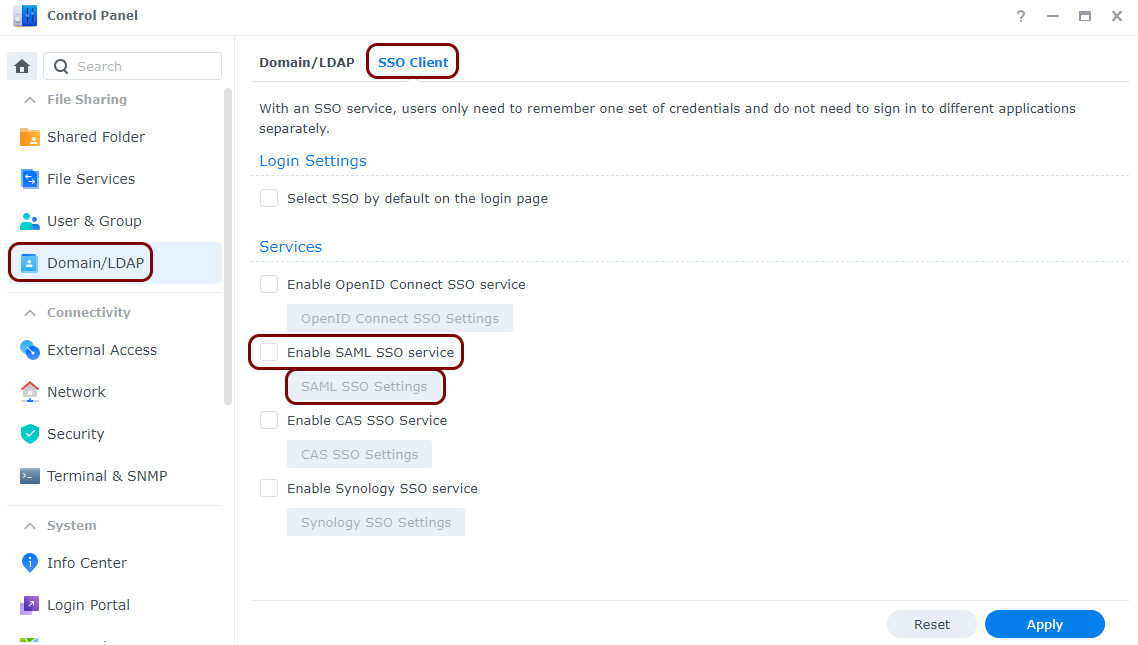
Open your Synology SAML authentication setup page
In this section, you will access your Synology administrative interface and find the SAML authentication setup page.
Enter configuration values in the Portnox tab
In this section, you will enter configuration values in the relevant fields in Portnox Cloud.
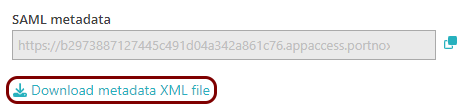
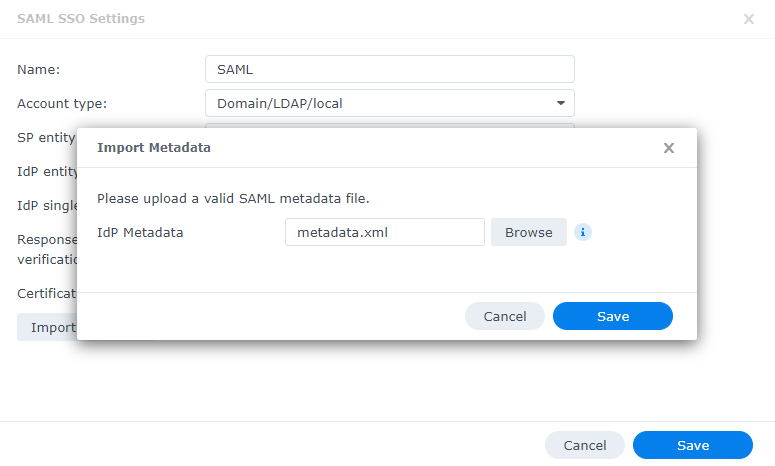
Export metadata from the Portnox tab and upload it in the Synology tab
In this section, you will export the metadata from Portnox Cloud into a file and upload that file in the Synology SAML setup section.
Finalize the configuration
In this section, you will finalize the configuration in Portnox Cloud and Synology.
-
Finalize the configuration in the Portnox tab.
-
Finalize the SAML configuration in the Synology tab.
Result: You have configured your Synology NAS to be accessible using Portnox Zero Trust Network Access.